Hi! I’m Firas Ben Nacib
Cloud & DevOps Engineer
Tunisia
Kubestronaut | AWS, Azure, Kubernetes, Terraform & Red Hat Certified
Loves Infrastructure as Code
About Me

Hey! I'm Firas, a Cloud & DevOps Engineer who loves AWS and tries to automate everything. I'm always building solid CI/CD pipelines, managing infrastructure with Terraform and Ansible, and exploring Kubernetes and GitOps to make life easier. I've also worked a bit with Azure, but AWS is where my heart is. I enjoy solving real problems and making technology work seamlessly.
Projects
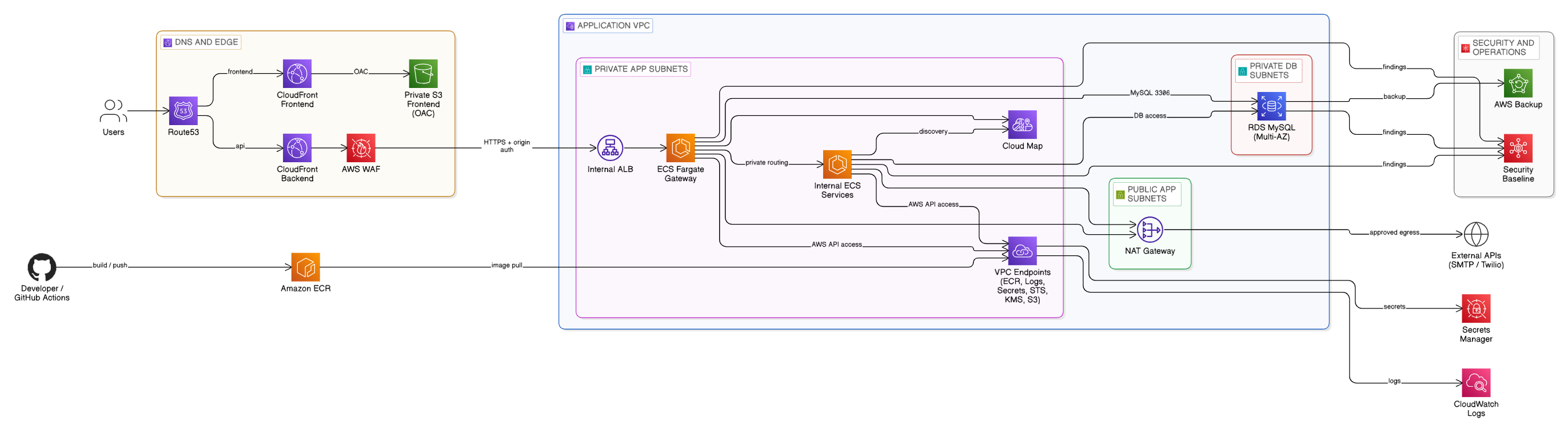
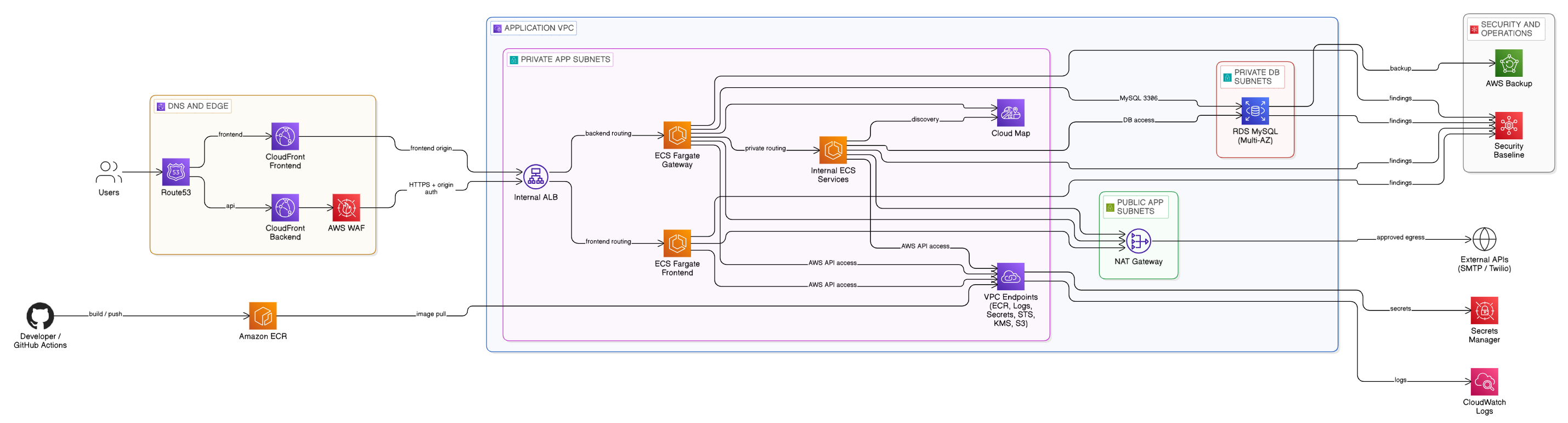
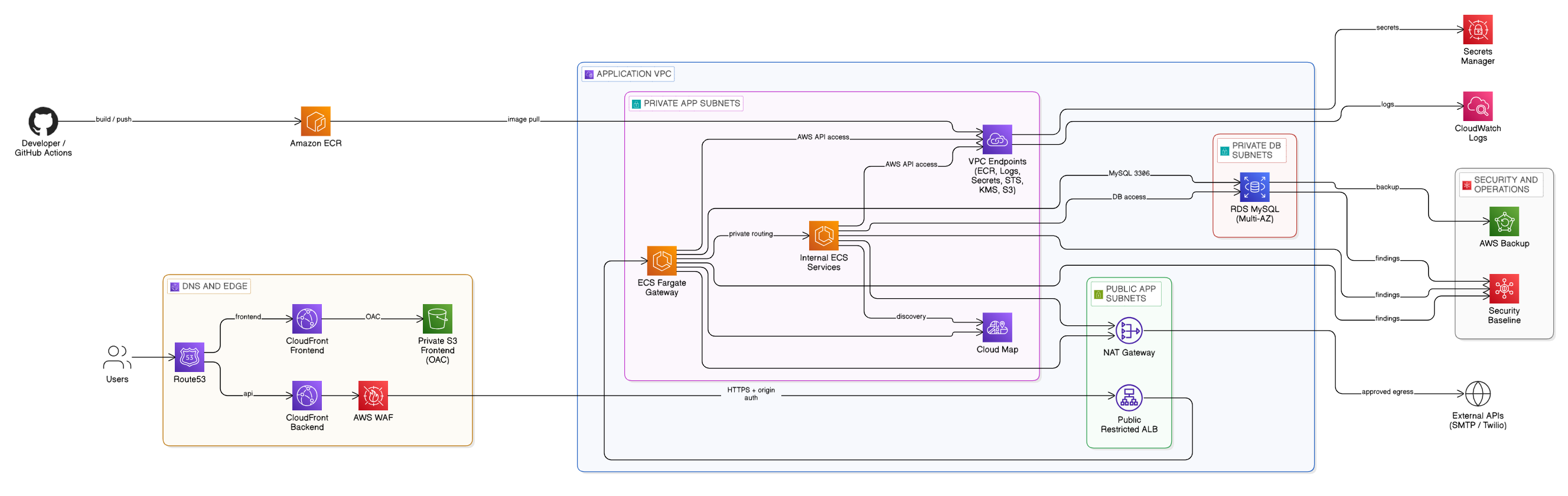
Terraform blueprint for private web apps on ECS Fargate, with two frontend options: a private S3 site behind CloudFront or a frontend served from ECS through the same CloudFront layer.
API traffic can stay fully private through CloudFront to an internal ALB, or use a public ALB restricted to CloudFront for services that need controlled public ingress. The blueprint also keeps RDS private, uses VPC endpoints and controlled outbound access, and adds GitHub Actions validation, drift detection, runtime checks, and IaC security scanning.
Tools: AWS (ECS Fargate, CloudFront, WAF, ALB, Route 53, S3, ACM, RDS, Cloud Map, CloudWatch, VPC Endpoints, NAT, AWS Backup, Secrets Manager), Terraform, GitHub Actions, Terratest, Infracost, TFLint, Checkov, tfsec, Snyk, Bash, Python
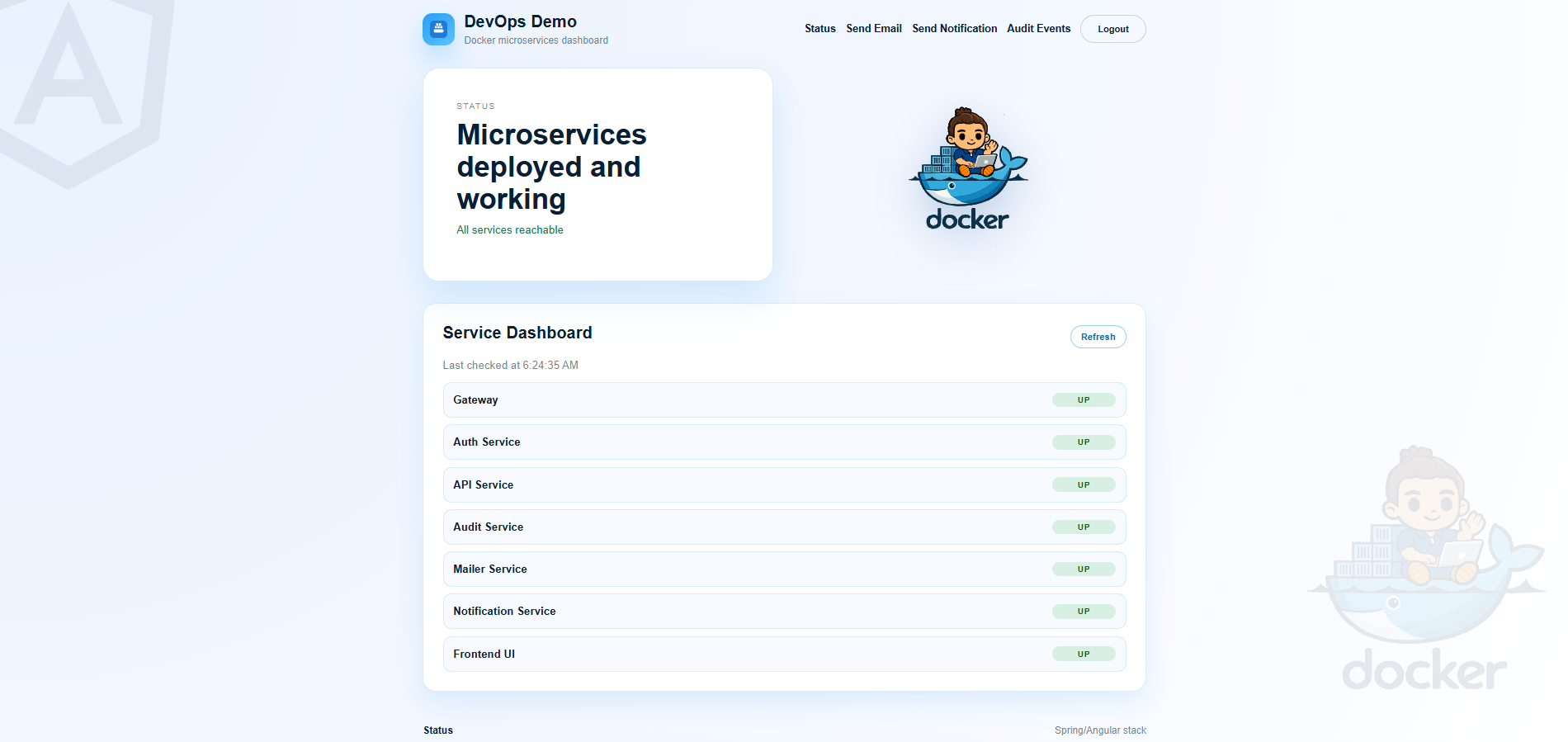
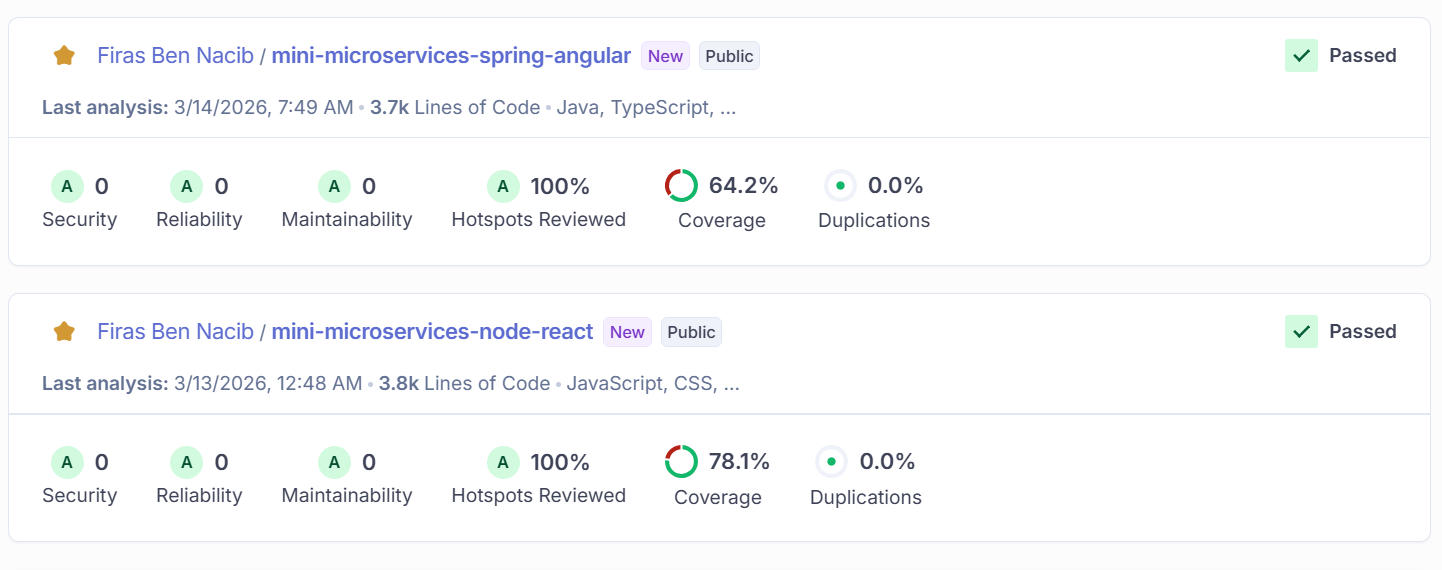
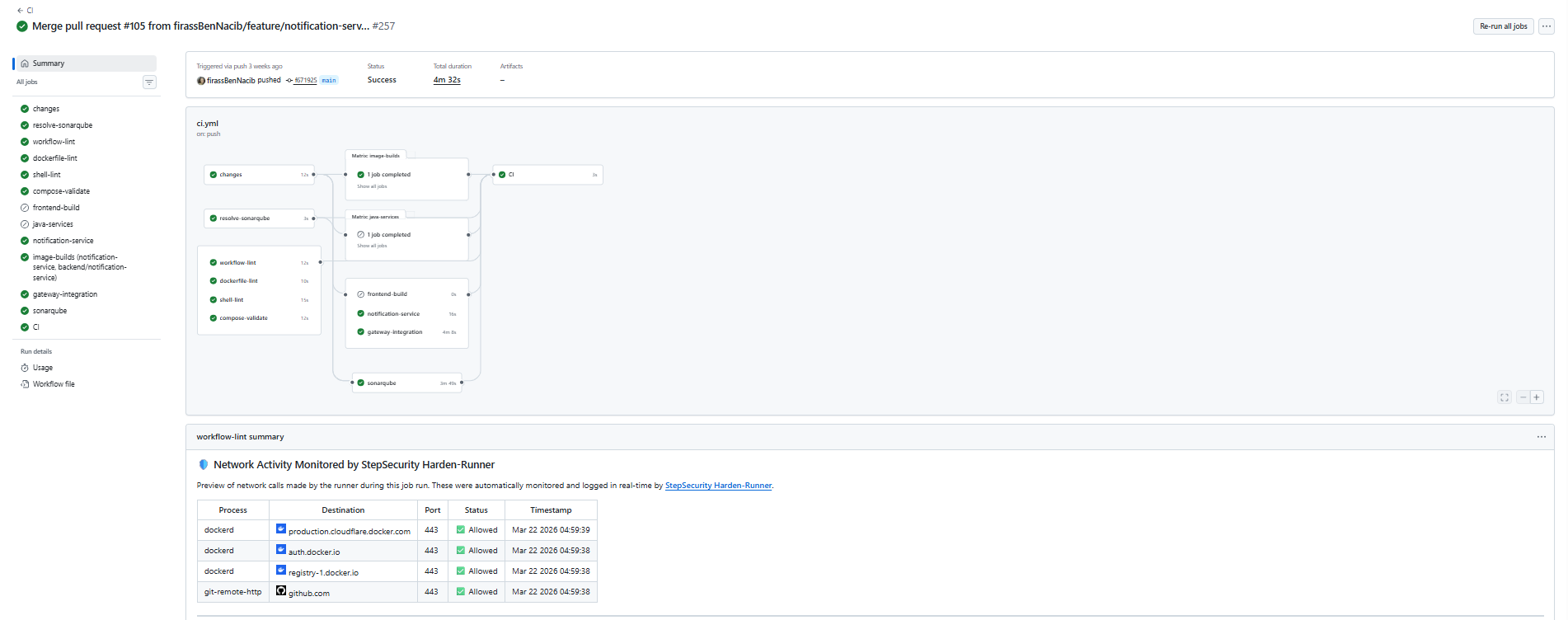
Two implementations of the same microservices platform: Spring Boot with Angular and MySQL, and Node.js with React and Postgres, both exposed through Nginx with dedicated auth, API, and audit services plus a shared FastAPI notification worker for SMTP and Twilio delivery.
Both repositories emphasize a full DevSecOps flow, combining CI/CD, SCA and dependency review, SAST with CodeQL, secret and configuration scanning, SBOM generation, image analysis with Trivy and Grype, DAST with OWASP ZAP and optional Nuclei, signed releases, smoke and integration tests, SonarQube quality gates, and object-storage deployment for the Spring/Angular frontend.
Tools: Spring Boot, Angular, Node.js, React, Python, FastAPI, Nginx, Docker Compose, MySQL, PostgreSQL, DevSecOps (SCA, SAST, DAST, SBOM, container scanning, signed releases), SonarQube, GitHub Actions, GitHub Dependency Review, Snyk, CodeQL, Gitleaks, Trivy, Grype, OWASP ZAP, Nuclei, OSSF Scorecard, Docker Hub, Amazon ECR, S3
AWS EKS platform with private networking and reusable Terraform modules for consistent infrastructure provisioning. Core workflows cover GitOps delivery with Argo CD and Helm, CircleCI release updates, Karpenter scaling, and cluster monitoring.
Tools: AWS (EKS, EC2, VPC, ALB, ECR, IAM/IRSA, Route 53, ACM, CloudWatch), Terraform, Kubernetes, Helm, Argo CD, CircleCI, Karpenter, ExternalDNS, Fluent Bit, Prometheus, Grafana, Trivy
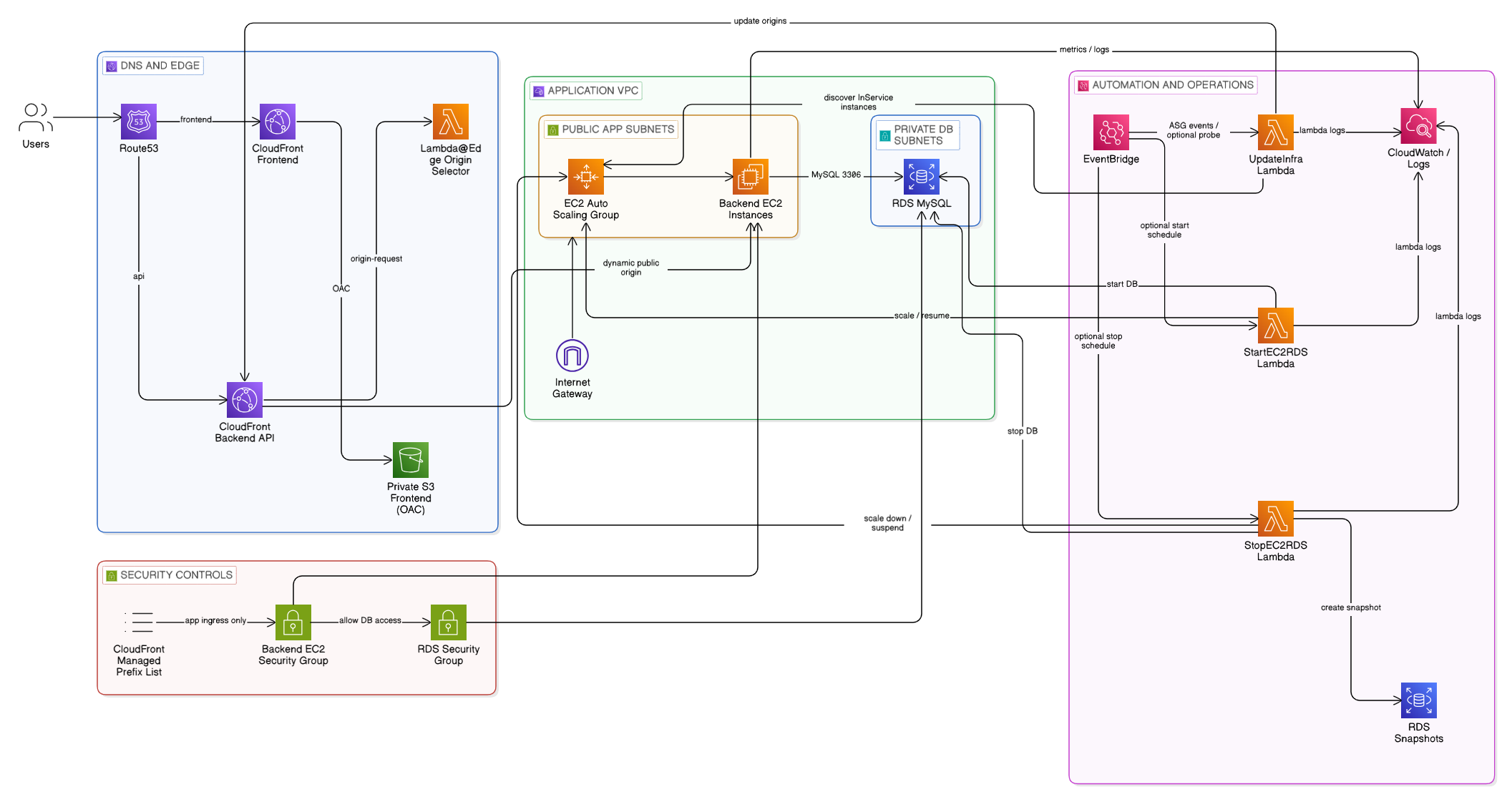
Modular Terraform architecture for cost-optimized AWS hosting, combining EC2 Auto Scaling, RDS MySQL, private S3 behind CloudFront OAC, Route 53, IAM, and Lambda@Edge to route requests to active instances.
Event-driven automation keeps origins in sync, supports optional EC2 and RDS scheduling, cleans up snapshots, and handles failure paths, with optional AWS WAF, origin-auth headers, observability add-ons, SQS and DLQ support, GitLab CI IaC checks, and configurable cost-saving profiles.
Tools: AWS (EC2, Auto Scaling, RDS, S3, CloudFront OAC, Lambda, Lambda@Edge, Route 53, ACM, IAM, CloudWatch, EventBridge, SQS, DLQ, WAF), Terraform, GitLab CI, TFLint, tfsec, gitleaks, Docker
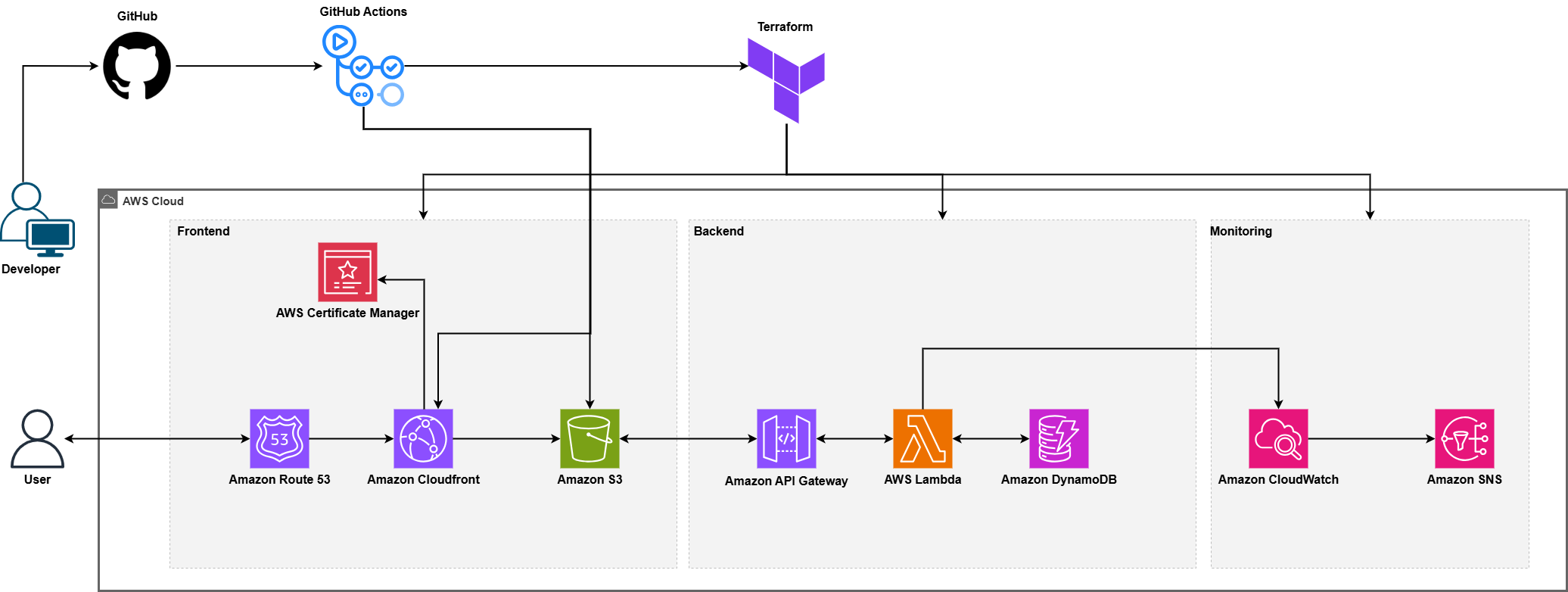
Cloud Resume Challenge website on AWS with global delivery, custom-domain TLS, and a serverless visitor counter.
The setup includes GitHub Actions pipelines, CloudWatch metrics, and SNS alerts for deployment and runtime checks.
Tools: AWS (S3, CloudFront, ACM, Route 53, Lambda, API Gateway, DynamoDB, CloudWatch, SNS, IAM), Terraform, GitHub Actions
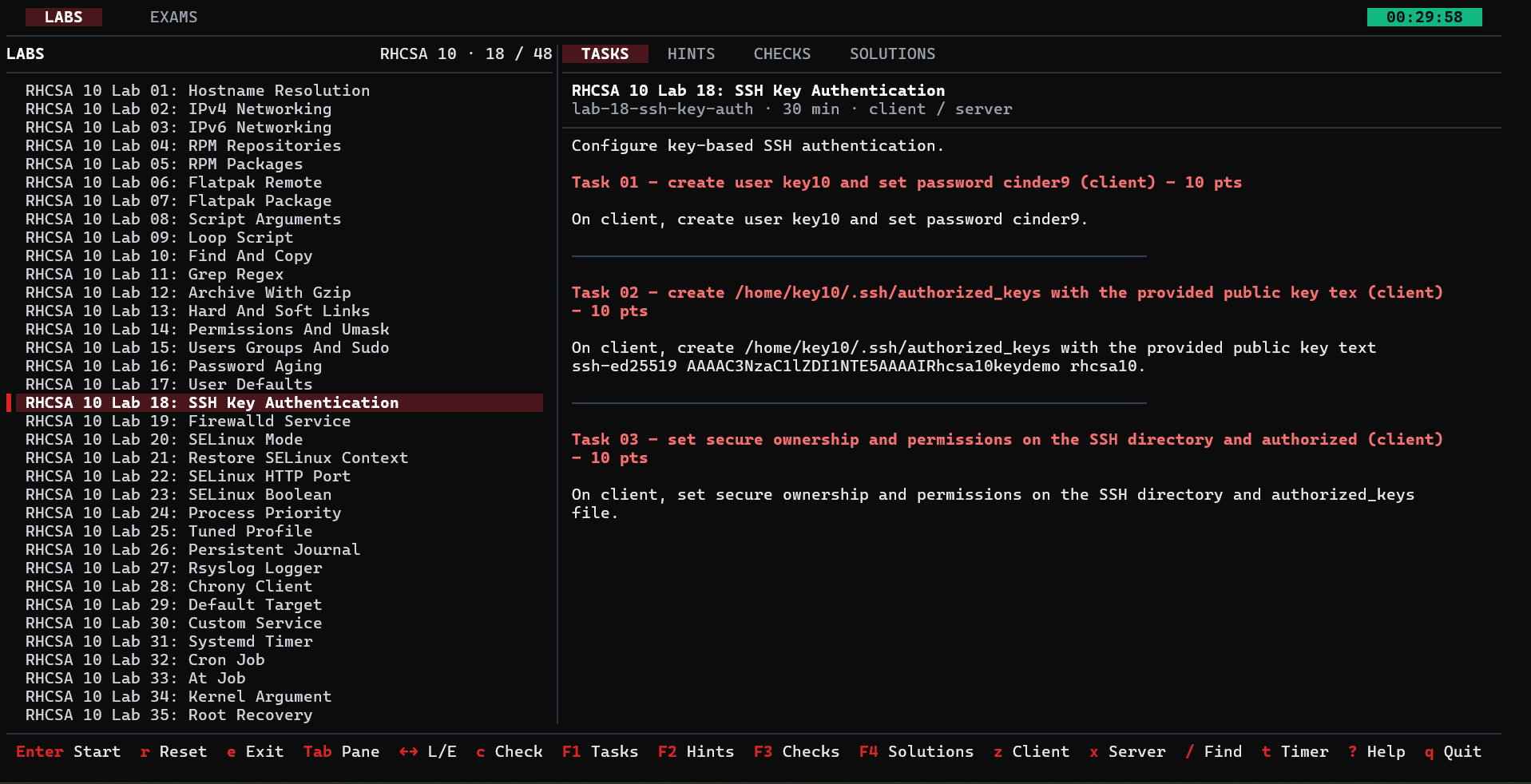
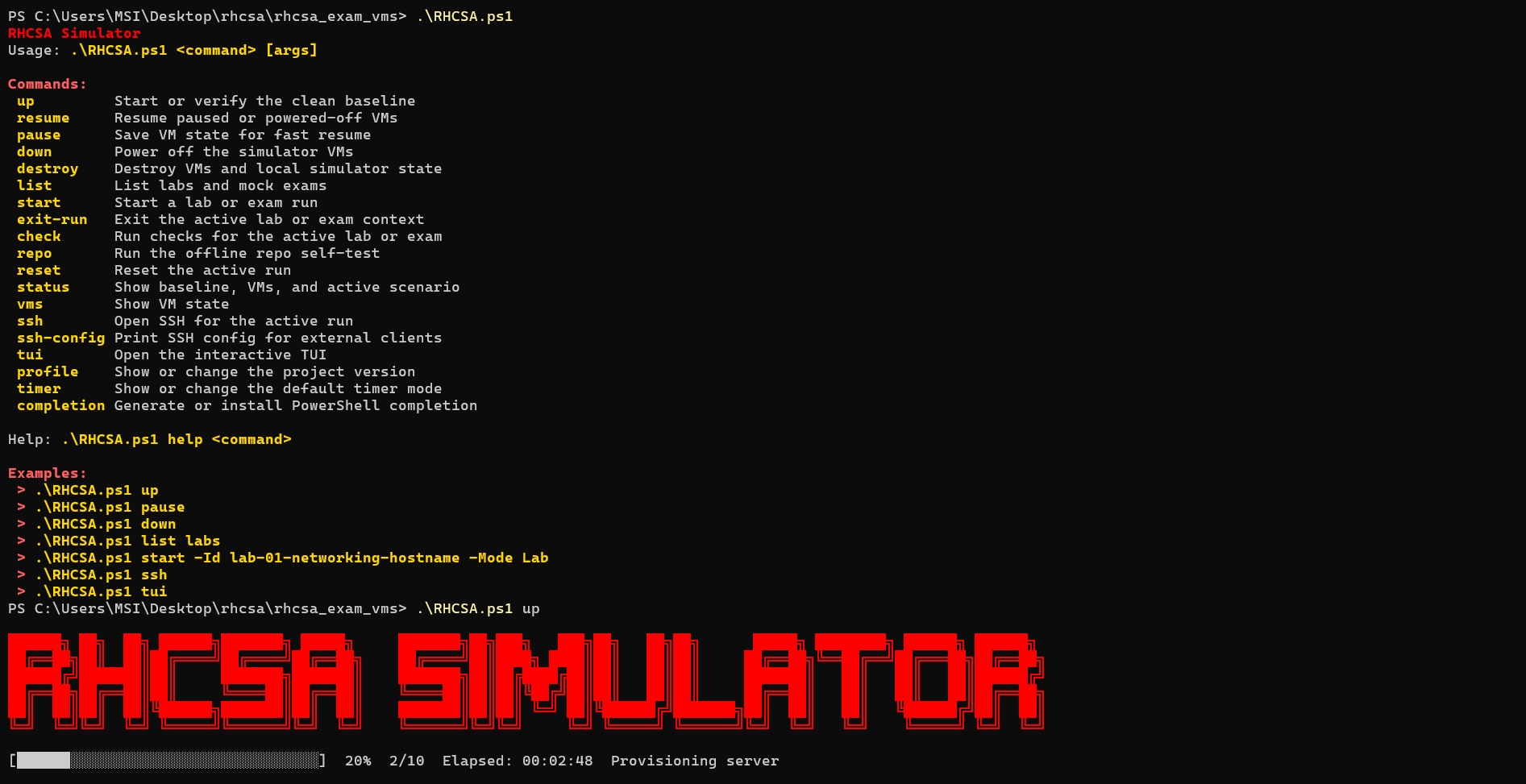
Interactive PowerShell simulator for RHCSA practice labs and mock exams, built around paired Vagrant and VirtualBox VMs with SSH helpers, run lifecycle controls, automated checks, and a terminal UI.
The project keeps RHCSA 9 and RHCSA 10 tracks separate, supports pausing and resuming active runs, and ships a TUI plus installer flow so learners can launch labs, review tasks and hints, run checks, and train against the right objective set.
Tools: PowerShell, Python, Go, Vagrant, VirtualBox, RHEL, GitHub Actions, GoReleaser

Interactive PowerShell script to create and bootstrap Talos Linux Kubernetes clusters on Hyper-V.
Tools: PowerShell, Talos Linux, Kubernetes, Hyper-V

PowerShell tool to create and manage local k3s Kubernetes clusters on Ubuntu Multipass VMs.
Tools: PowerShell, k3s, Kubernetes, Multipass, Hyper-V, Ubuntu VMs
Messaging prototype based on Spring Boot and ActiveMQ, containerized with Docker and released through Jenkins quality gates. Its deployment flow combines Kubernetes scaling, delivery workflows, and alerting hooks for service operations.
Tools: Java, Spring Boot, Maven, ActiveMQ, Docker, Jenkins, Kubernetes, KEDA, Argo CD, Prometheus, Grafana Alerts, SonarQube, Weka
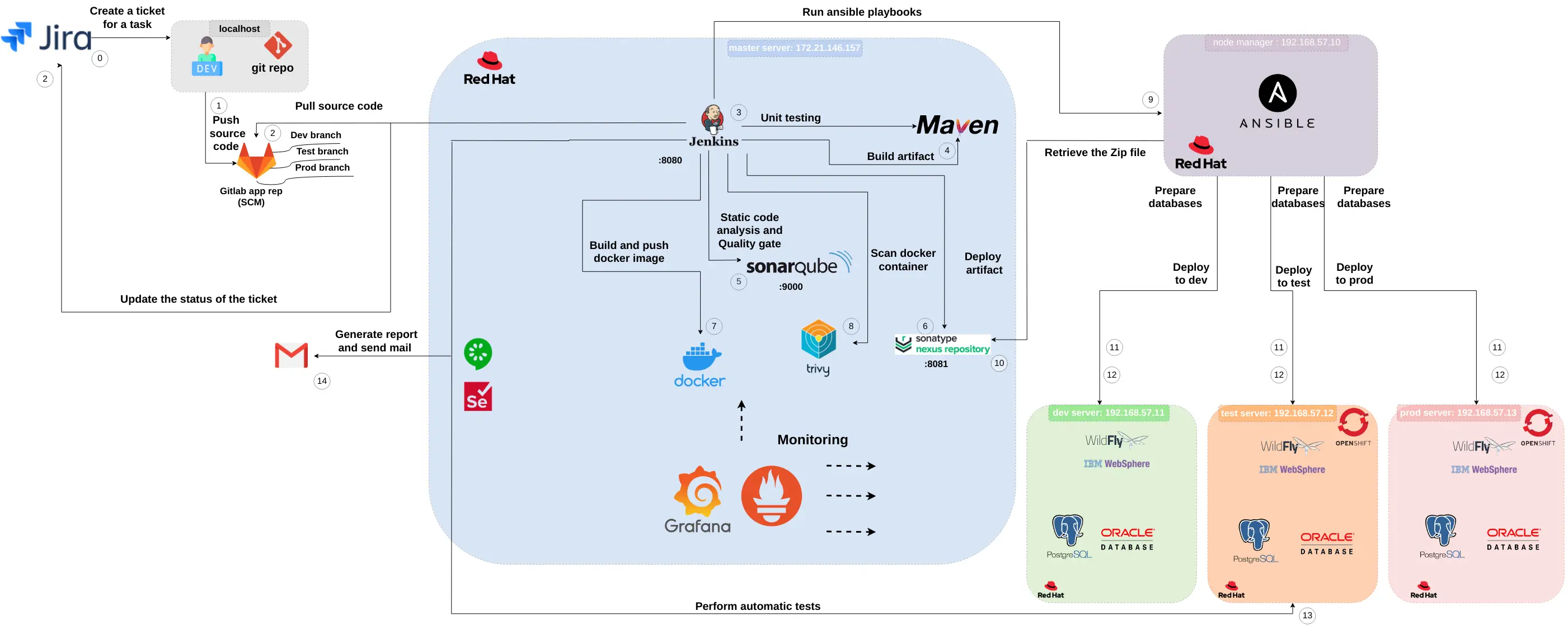
Enterprise CI and deployment architecture connecting Jira and GitLab to Jenkins and Maven build stages, SonarQube quality gates, Docker and Trivy image workflow, Nexus artifact delivery, Ansible deployments to dev, test, and prod OpenShift servers, and Prometheus and Grafana monitoring.
Tools: Jira, GitLab, Jenkins, Maven, SonarQube, Docker, Trivy, Nexus Repository, Ansible, OpenShift, WildFly, IBM WebSphere, PostgreSQL, Oracle Database, Prometheus, Grafana, Selenium
Skills
Cloud & Infrastructure
Containers & Orchestration
Monitoring & Logging
Databases & Servers
Linux Distributions
Security
Languages & Scripting
Virtualization & Platforms
Certifications

Kubernetes and Cloud Native Security Associate (KCSA)
Issued by The Linux Foundation
View Credential